Ryan Haines/Android Authority
TL;DR
- Galaxy S22 Ultra owners are finding their retail phones claimed by a suspicious company called “Numero LLC” after performing a factory reset.
- The lockout occurs through Samsung’s servers at the IMEI level, which means that factory reset and manual firmware flashing cannot bypass it.
- Affected users are stuck between Samsung and Knox support teams, neither of whom currently claim to have the tools to fix the record.
Samsung Galaxy phones are among the best phones you can buy for enterprise use, thanks to features like hardware root of trust via Knox Vault, an immutable e-fuse to detect firmware tampering, and more. knox suite For managing large scale devices. But over the past few months, non-enterprise users have been facing a “digital brick” scenario that weaponizes some of these features, effectively locking them out of their phones.
“This device is not private” trap
We’ve seen several Galaxy S22 Ultra owners complaining (1, 2, 3, 4) that their phones are reportedly locked after a factory reset.
The sequence is almost the same in every case: After the reset, users connect to Wi-Fi to begin the standard Android setup. However, before they can sign in to their Google account, they are put on hold knox mobile enrollment (KME) Provisioning screen with the message “This Galaxy S22 Ultra is not private”, stating that the phone is managed by an organization and all data and activity is visible to a remote IT administrator.
However, the key point here is that the phones are reportedly not provided through any organization and are not part of the corporate fleet. These phones were said to be purchased through standard retail channels through Samsung, with no affiliation or connection to any company.
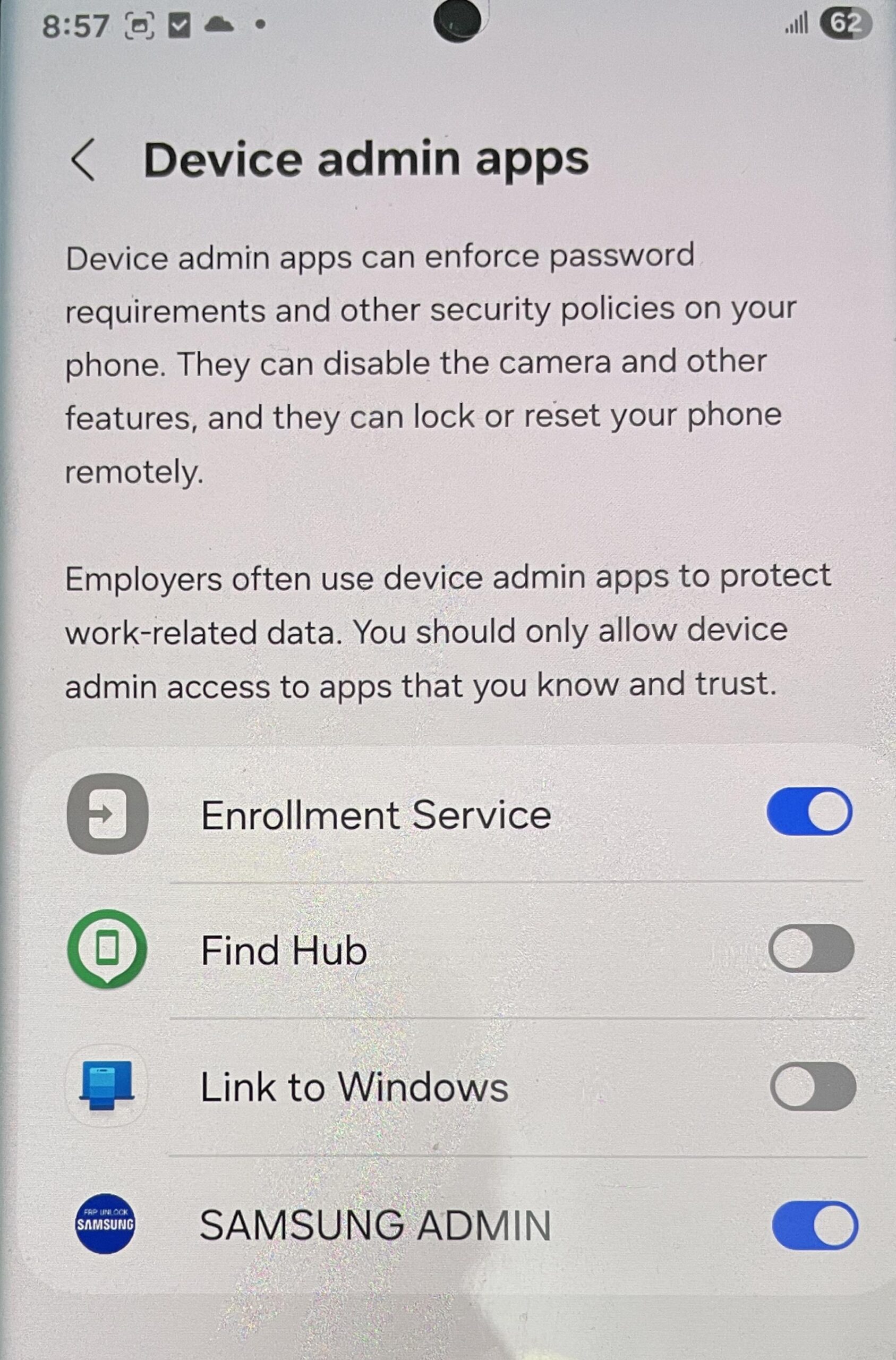
There are some clear indications that it is suspicious. For starters, the title of the admin app is “Samsung Admin” in capital letters, and the logo says “FRP Unlock Samsung”. The company mentioned is “Numero LLC”, which does not appear in US company records (one of the screenshots shows “5G UC”, meaning the phone is on T-Mobile’s “Ultra Capacity” network, and thus located in the US), although we could. Find a link to South Korea.
Don’t want to miss the best of Android Authority?


Factory reset won’t help you get your phone back
Users have tried bypassing it by doing multiple factory resets and even manually flashing the firmware with Odin, but the lock remains. This is because the handshake happens at the IMEI level.
When the phone pings Samsung’s attestation servers during setup, the servers check their databases and see that the IMEI is “claimed” by Numero LLC. It then sends a mandatory MDM (Mobile Device Management) profile to the phone. Because this happens at the firmware level within the setup wizard, the user is stuck in a “Catch-22”: accept a compromised phone with a remote “ghost” admin, or end up with a phone that can’t be activated or used.
Another possibility is that attackers may have taken advantage of recent vulnerabilities in Knox. CVE-2026-20978Seen in KnoxGuard, which allows unauthorized parties to bypass ownership checks and tamper with enterprise management settings. However, this requires physical access to the phone at some point.
The “FRP Unlock” branding also suggests that these hijackings may be a side effect of users previously using questionable third-party unlocking services that may have used their IMEI.
If you find yourself at this screen, your only legitimate recourse is to contact Samsung Support with your original proof of purchase and ask for “IMEI Enrollment”. However, users report getting stuck in a support loop: Samsung support redirects them to Knox technical teams, claiming they lack the tools to modify enterprise records, and then redirects them back to Samsung support. So prepare yourself for a phone that is digitally ready.
We’ve contacted Samsung to learn more about this issue. We will keep you updated when we hear back from the company.
Thank you for being a part of our community. Please read our comment policy before posting.

